A security analyst is investigating an incident related to an alert from the threat detection platform on a host (10.0.1.25) in a staging environment that could be running a cryptomining tool because it is sending traffic to an IP address that is related to Bitcoin.
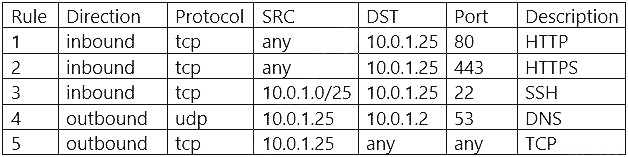
The network rules for the instance are the following:
Which of the following is the BEST way to isolate and triage the host?
A. Remove rules 1, 2, and 3.
B. Remove rules 1, 2, 4, and 5.
C. Remove rules 1, 2, 3, 4, and 5.
D. Remove rules 1. 2, and 5.
E. Remove rules 1, 4, and 5.
F. Remove rules 4 and 5.
The network rules for the instance are the following:
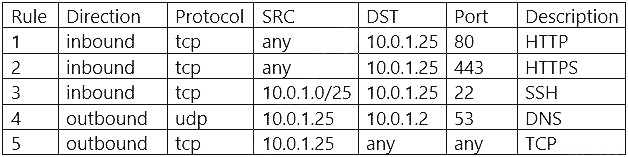
Which of the following is the BEST way to isolate and triage the host?
A. Remove rules 1, 2, and 3.
B. Remove rules 1, 2, 4, and 5.
C. Remove rules 1, 2, 3, 4, and 5.
D. Remove rules 1. 2, and 5.
E. Remove rules 1, 4, and 5.
F. Remove rules 4 and 5.